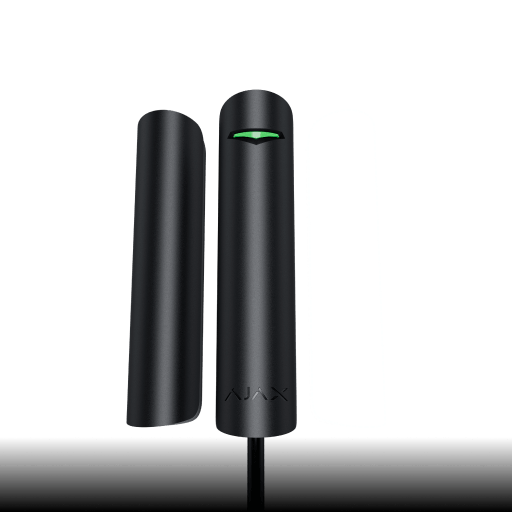
Superior DoorProtect G3 Fibra
Wired opening, shock, and tilt detector
Product is not available in your region
Guardian for doors, windows, and valuables
Superior DoorProtect G3 Fibra is designed to detect intrusion and burglary attempts, offering comprehensive coverage for doors, windows, skylights, and vaults. The detector is equipped with two reed switches as opening sensors and a magnetometer for protection against magnet spoofing. Two sizes of magnets provide more mounting options. The device also identifies shock and tilt with a built-in accelerometer, protecting the facility even when windows are in airing mode. All in line with the Ajax user experience, ensuring quick and easy installation of the device.
Discover Superior DoorProtect G3 Fibra
Introducing expanded features of Fibra product line
Watch on YoutubeKey features
In an Ajax system, you can combine devices of all product categories: Intrusion protection (both Superior and Baseline), Video surveillance, Fire and life safety, or Comfort and automation. Create the system to suit your needs and manage it in a single interface.
This is the device of the Superior product line. Only accredited Ajax Systems partners can sell, install, and administer Superior products.
Protection for high-security facilities
Future-proof hardware
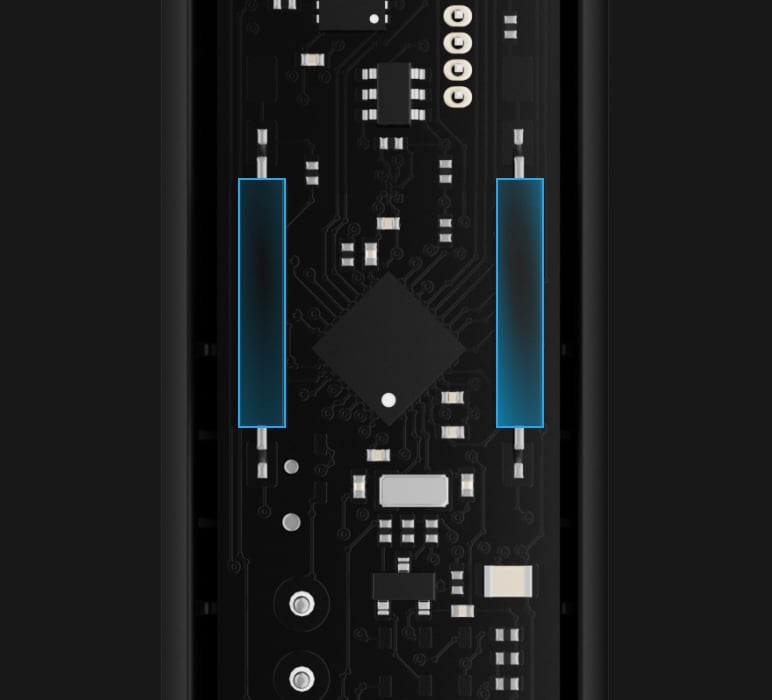
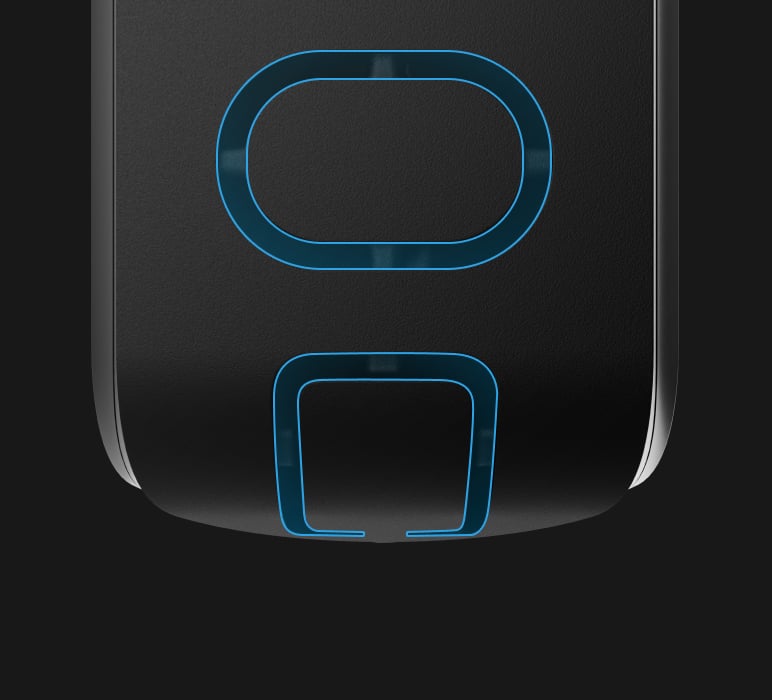
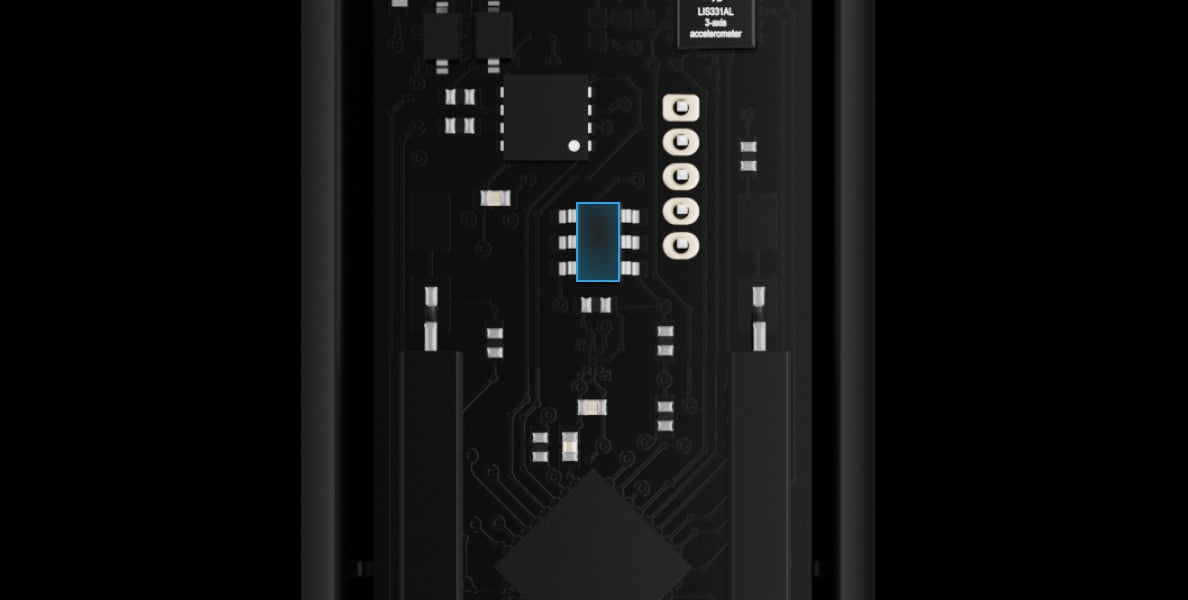
Two reed switches
Accelerometer

Holding screw to secure the detector’s casing

Removable device board

Tamper against casing disassembling

Tamper against detaching the detector from the surface
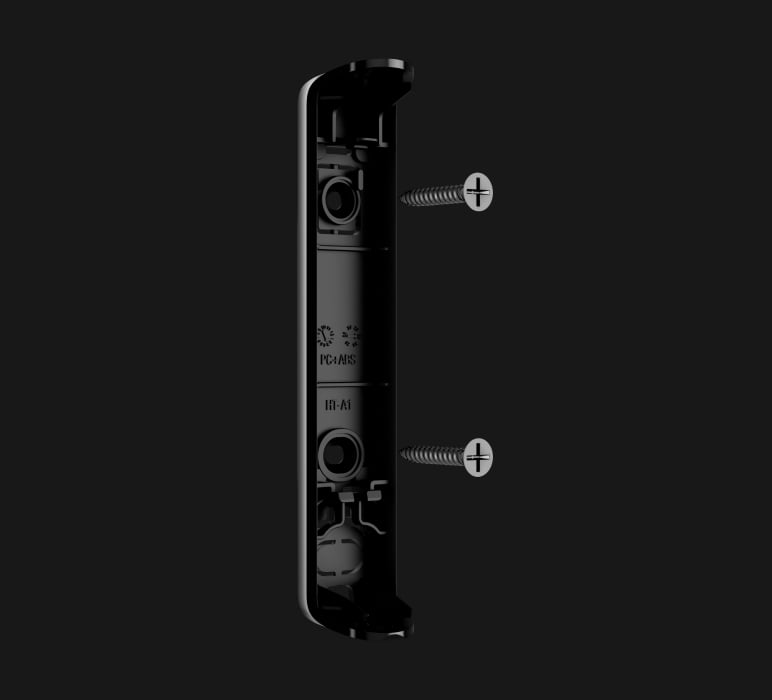
Fixing points for mounting the detector
Perforated parts for wire routing
No intruder goes unnoticed
High-end reed switches for reliable opening detection
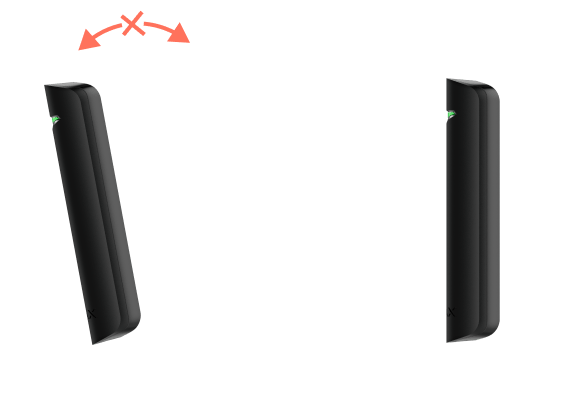
Superior DoorProtect G3 Fibra features two durable reed switches, guaranteeing decades of trouble-free operation. Two reed switches allow the magnet to be positioned on either side of the sensor (right or left). Housed in resilient plastic capsules, these switches remain intact even in cases of drops or transportation, ensuring the detector’s effective functionality irrespective of magnet placement.
Effective detection wherever the magnet is placed — left or right
Plastic capsules for protecting reed switches during transportation
Magnetometer prevents sabotage
The integrated high-end magnetometer records local magnetic field data during calibration, allowing the sensor to identify and monitor the installed magnet. Immediate alarms are triggered by any changes in the magnetic field, providing protection against magnet spoofing. The straightforward calibration process and adjustment of sensitivity levels in the app ensure precise interference detection and eliminate false alarms. Plastic spacers in the mounting kit reduce the impact of metal surfaces when the detector is installed, for example, on the vault door.
Magnetometer for interference detection
Calibration of the magnetometer for high accuracy
Plastic spacers for mitigating interference from metal surfaces

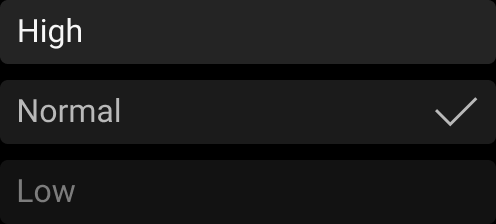
Immediate detection of threats
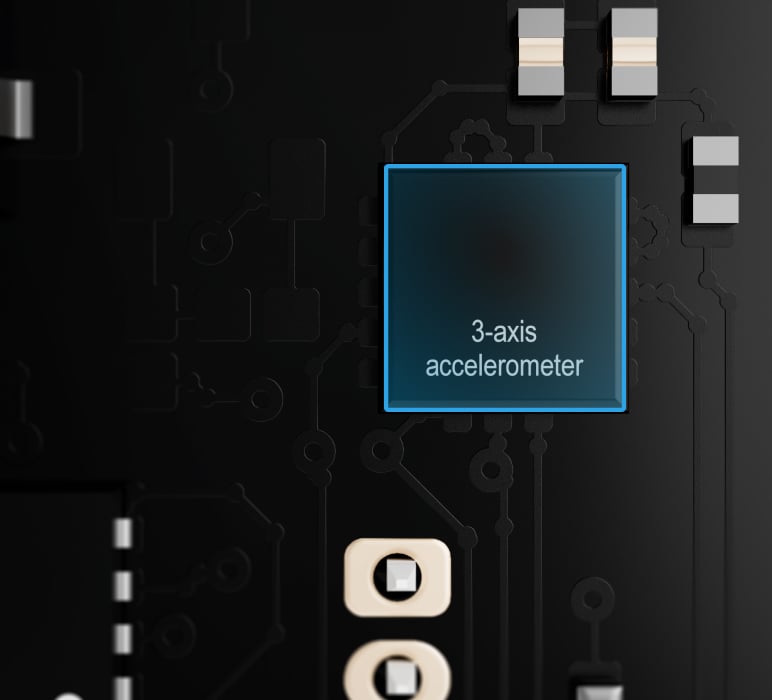
The built-in accelerometer responds swiftly to shocks, detecting potential burglary attempts such as door forcing and vault breaking. The shock sensor has three levels of sensitivity, which can be adjusted to match the secured facility specifics. The detector can also ignore a single impact to minimize the risk of false alarms triggered by external factors. Whether there are vibrations from neighboring constructions or heavy passing traffic, the installer can choose the most appropriate settings for accurate detection.
Early identification of threats through shock detection
Three sensitivity levels
Single shock ignoring to prevent false alarms

Windows protection in an airing mode
The built-in accelerometer is designed to protect open windows, seamlessly adapting to diverse facility requirements. Installers can select a normal tilt angle for doors or windows, ranging from 5 to 25 degrees. The system swiftly detects even the slightest deviations from the usual position and provides customizable tilt detection durations, ranging from 1 second to 1 minute. In case the tilt angle surpasses the specified threshold for an extended period, the system raises an alarm.
Tilt detection
Selection of the normal tilt angle
Adjustable time of alarm

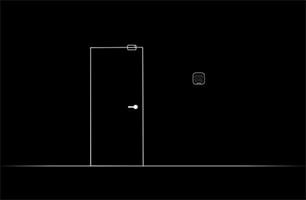
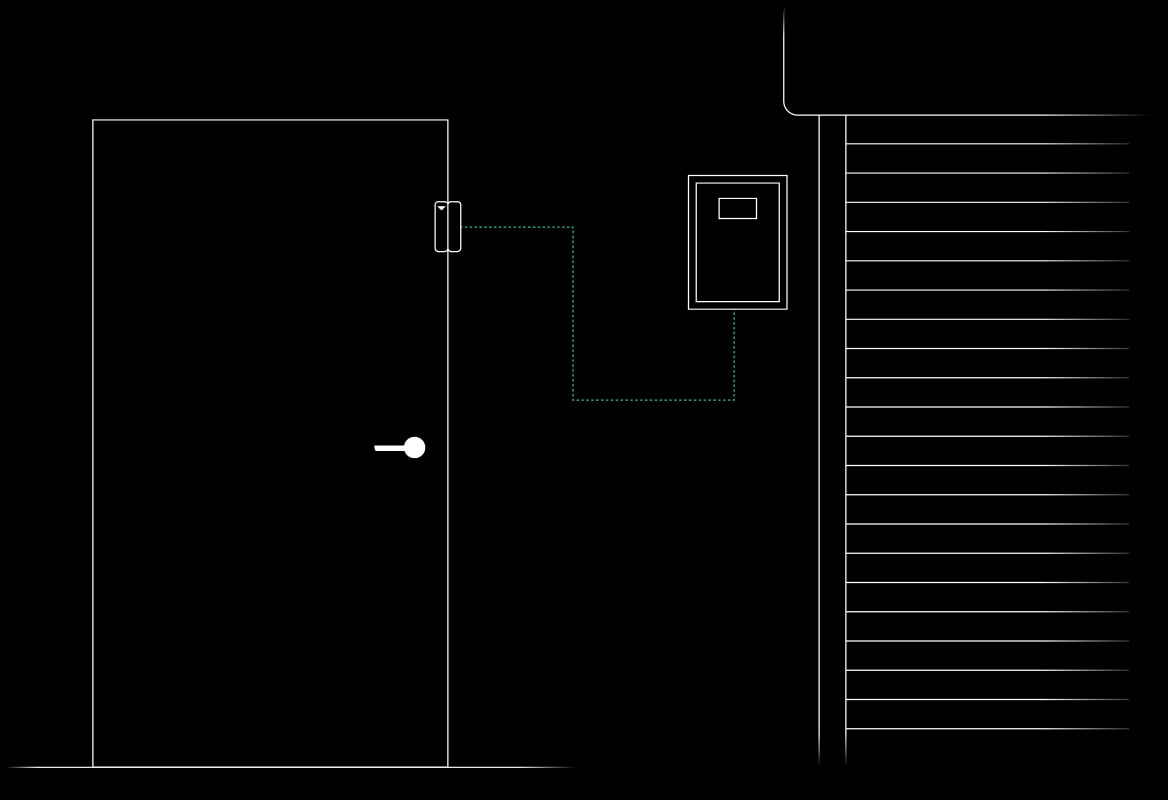
Enhanced security with additional detectors
Superior DoorProtect G3 Fibra has terminals for connecting any third-party wired NC detector, enhancing the reliability of the entire system. For example, an installer can integrate an additional detector operating on a different principle, such as a roller shutter motion detector. When connected to Superior DoorProtect G3 Fibra, it promptly responds to alarms from detectors and cable breakage³.
Use a detector as a doorbell
The Chime feature transforms the combination of an Ajax opening detector and Ajax siren into a shopkeeper's bell. When the system is disarmed, the siren notifies about door openings with one of four available short beep patterns. Pro users can choose the volume of sound, and different patterns can be assigned for separate entrances, making it easy to recognize whether someone entered through the main or a back door.
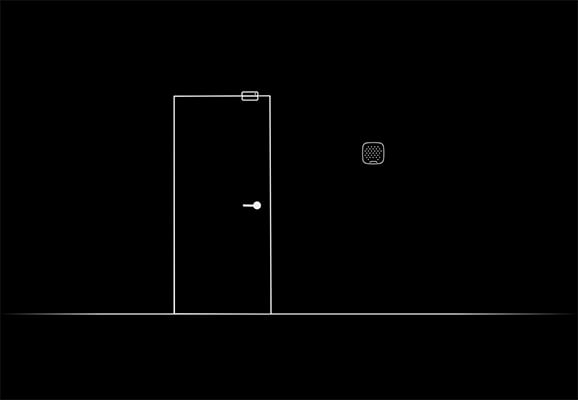
Door opening sound signals
Setting up signals for different security groups
Customizable signals for separate entrances
The system needs to contain a siren for the Chime feature to work.

System supervision
All Ajax devices perform automatic self-diagnosis and report their states to the hub. Essential parameters, including tamper, communication, power supply, and sensor statuses, are continuously monitored. The Ajax Cloud server controls communication between the hub and Ajax apps, ensuring instant notifications for ARCs, security companies, and users. In case of any malfunction or communication failure, an engineer is promptly informed to provide necessary services.
Automatic device self-diagnosis with status report
Regular polling to display the current device state on apps
Instant maintenance notifications

Fibra
Unique wired technology
Fibra is Ajax’s proprietary technology for secure two-way communication between devices and a hub or module that extends the Fibra line. Fibra features encryption and device authentication to prevent sabotage, spoofing, and data theft. The Fibra line supports all types of devices, including sirens, keypads, and detectors with photo verification.
Communication range of up to 6,550 ft
One Fibra line for different device types
Photo delivery via Fibra line without interference
Protection against sabotage and spoofing
Energy efficiency as a priority
Fibra communication requires minimum power consumption, with the module consuming only up to 0.035 W at its peak. Fibra operates on the TDMA principle. Each device has a short time frame to exchange data with a hub, and its communication module remains inactive the rest of the time. This significantly reduces power consumption and helps avoid interferences even when multiple devices communicate simultaneously.
Detector power consumption is up to 0.035 W
TDMA and power-saving modes
Sabotage resistance





Next-level protection of Fibra line
Introducing LineProtect, the module designed to protect an Ajax hub and connected wired devices from sabotage when intruders cause overvoltage, short circuits, apply 110/230 V~, or use stun guns.
PRO is king
The myth about wired systems being difficult to install is busted. Ajax minimized an expensive, long, and dusty experience for PROs by developing an ultimate set of tools to make the process easy and flexible, from project design to client support and system maintenance. Everything for smooth and quick installation is included. Intuitive Ajax apps help make the device a part of the system, and each device can be reconfigured remotely at any moment. No need for programmers — everything is available out of the box.
Fibra power supply calculator
The online tool provides security engineers with detailed data on devices' power consumption, enabling easy pre-installation assessment of the wired system project. It helps design the project in real time, highlights problem spots, and offers solutions. Upon completion, results can be downloaded as a PDF file.
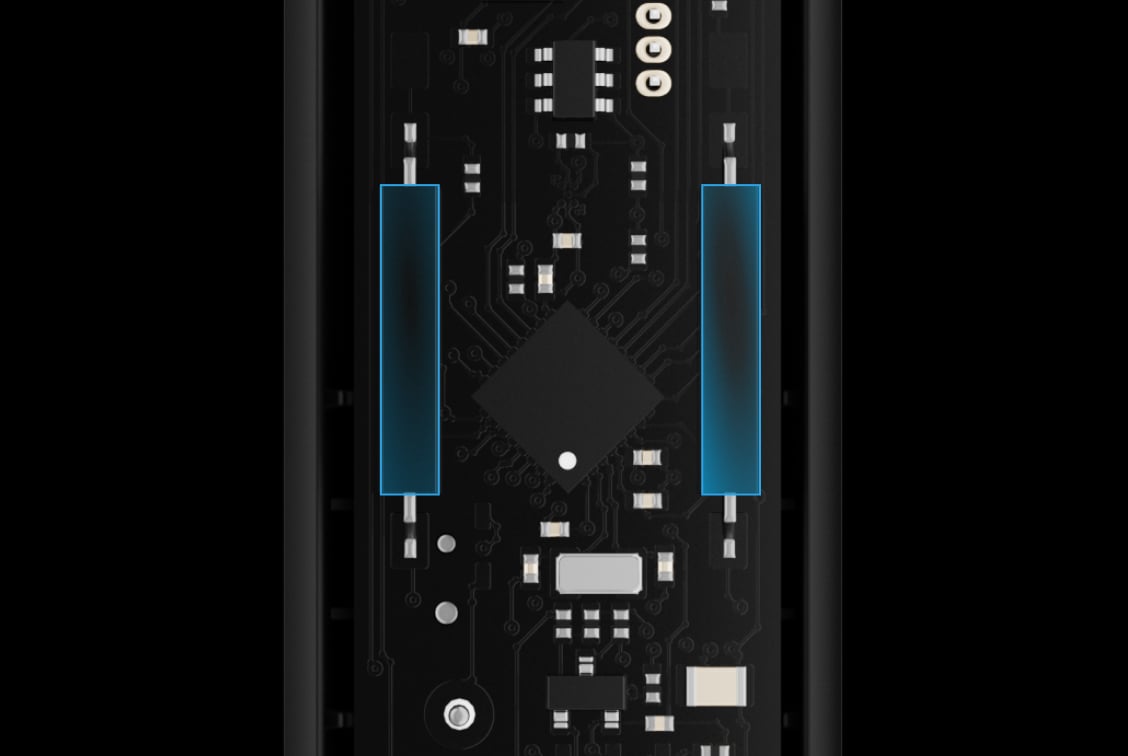
The installation kit includes all the necessary fasteners. The device board is removable, which makes the connection process more comfortable. For cable management, there are several perforated parts for cable routing.
Removable device board
All the necessary fasteners included in the installation kit
Holding screw to secure the device on a mounting panel

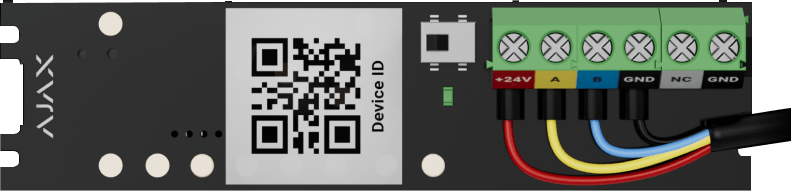
The device is paired with the hub automatically via Fibra line scanning. This tool is available in the desktop or mobile PRO apps. An installer only needs to name the device and assign it to the room and security group. The device can also be added by scanning the QR code or entering its ID manually.
Pairing with a hub via automatic line scanning or QR code
Device identification via triggering or LED indication
Optimal default settings to cover major requests

Intuitive Ajax apps provide remote set-up and testing with all device information from anywhere the Internet is available, on a smartphone or PC. An installer can remotely change the settings and provide services promptly without visiting the object.
Configuration and testing remotely or on site
iOS, Android, macOS, and Windows apps
Accounts for companies and installers
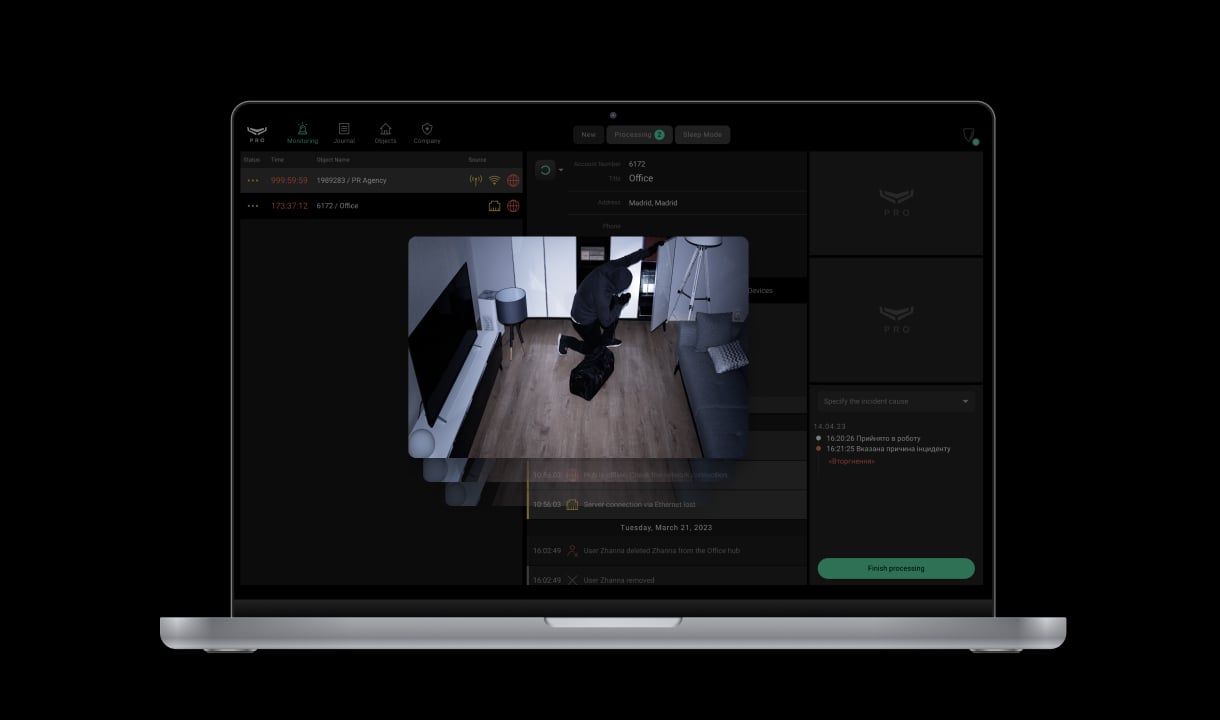
An Ajax system transmits alarms to the PRO Desktop monitoring app or any third-party CMS. The security company receives an alarm notification in less than a second. Notifications include all the necessary information: name of the device, time of the event, and the exact room where the device is located. The security company also receives photo or video verification, capturing the reason for the alarm.
Full addressability of connected devices
Instant in-app notifications
Alarm and event monitoring through Ajax PRO Desktop or third-party CMS
- 1 The Chime feature requires an Ajax siren to operate. Learn more about Chime.
- 2 With U/UTP cat.5, 4 × 2 × 0.51 cable. Other cable types may have different values. Please use Fibra power supply calculator to check the wired system project before installation.
- 3 A roller shutter can detect cable breakage, while an NC detector responds only to alarms.
- 4 The list of transmitted parameters may vary depending on the CMS type and selected communication protocol.
Technical information
Superior DoorProtect G3 Fibra
Ajax product categories
In an Ajax system, you can combine devices of all product categories: Intrusion protection (both Superior and Baseline), Video surveillance, Fire and life safety, or Comfort and automation. Create the system to suit your needs and manage it in a single interface.
Wired opening detectors Superior DoorProtect G3 Fibra
Advanced intrusion detection systems are one of the most effective ways to enhance security. Wired opening detectors have gained prominence among these systems due to their reliability, versatility, and robustness.
Wired security devices serve as the first defense against unauthorized access, providing invaluable peace of mind to property owners. These detectors are designed to monitor entry points such as doors and windows, utilizing various technologies to detect openings, vibrations, and other indicators of potential intrusion. Many current models feature state-of-the-art sensor technologies, which enable them to identify not only the opening of a door or window but also shocks and tilts. This added functionality is crucial in securing various premises, including residential homes, offices, retail stores, and high-security facilities.
One of the hallmark advantages of wired detectors, such as the Superior DoorProtect G3 Fibra, is their stability and dependability. Unlike their wireless counterparts, wired detectors are not susceptible to signal loss or interference, making them a preferred choice in areas where reliable communication is critical. These devices use low-voltage electrical systems to communicate with central monitoring units, ensuring continuous operation, even in adverse conditions.
Wired detectors are often equipped with features such as tamper alarms, which notify users if someone attempts to remove or disable them. Additionally, many models are designed with protection against environmental factors, ensuring their effectiveness in varying conditions. With regular maintenance, wired systems can provide decades of trouble-free operation, making them a sound investment for securing property.
Discovering the wired opening detector Superior DoorProtect G3 Fibra
The Superior DoorProtect G3 Fibra is a top-tier wired opening detector that epitomizes advanced security technology. Designed for a wide range of applications, this device detects openings, shocks, and tilts, providing comprehensive protection for various entry points. Its Grade 3 certification indicates that it meets stringent standards for reliability and security, making it suitable for high-security environments such as banks, museums, jewelry stores, medical facilities, and more.
Key features and benefits:
- Multi-functionality
The Superior DoorProtect G3 Fibra is more than just a simple opening detector. It includes advanced shock and tilt sensors, allowing it to monitor additional threats, such as forced entry through windows, even when they are in pairing mode. This flexibility ensures robust security coverage across any premises.
- High-end reed switch technology
Featuring two durable reed switches, this device provides reliable opening detection from multiple angles. This redundancy ensures the other can operate if one switch fails, enhancing overall reliability.
- Flexible installation options
The device comes with both small and large magnets, allowing users to customize the installation according to the configuration of their doors or windows. This adaptability ensures optimal performance regardless of layout limitations.
- Protection against false alarms
The Superior DoorProtect G3 Fibra has protective features that minimize the risk of false alarms due to environmental disturbances. This ensures that users are alerted only in genuine intrusion scenarios.
- Seamless integration with third-party detectors
The device includes terminals for connecting third-party wired NC (normally closed) detectors, significantly enhancing system reliability without additional power sources. This capability allows for integrating varied security solutions into one cohesive system.
- Extended battery life
Although wired detectors do not rely on battery power like wireless systems, their low power consumption design ensures that the device is energy-efficient. Typical operation consumes up to 0.035 W, translating to long-term reliability and functionality.
- User-friendly setup and operation
The SmartBracket mounting panel facilitates straightforward installation, minimizing assembly complexity. Despite this ease, professional installation is recommended to ensure optimal positioning and configuration, maximizing the detector's effectiveness.
- Real-time notifications and alerts
The system offers timely notifications through the Ajax app regarding openings, tampering events, or operational errors. This capability enables immediate user response to security incidents, further enhancing safety measures.
- Robust wired communication technology
Utilizing the Fibra proprietary protocol, the Superior DoorProtect G3 Fibra ensures secure, encrypted two-way communication with a range of up to 2,000 meters. This reliability is essential for locations with demanding security needs.
- Versatile applications for enhanced security
The Superior DoorProtect G3 Fibra is suitable for a wide array of applications. Whether securing a residential property, an office, a retail store, or a high-security facility, this detector provides consistent and reliable protection tailored to various operational needs. Its discreet design integrates seamlessly into any environment without compromising aesthetics.
Conclusion
By adopting the Superior DoorProtect G3 Fibra, you are proactively choosing to enhance the security of your home, business, or any valuable assets you wish to protect. This device is not only a guardian against unauthorized access but also a wise investment in the safety of your property.
Whether reinforcing security in residential settings, enhancing safety in commercial spaces, or safeguarding high-security environments, the Superior DoorProtect G3 Fibra stands out as an exceptional choice. Its advanced detection capabilities, low power consumption, and ease of integration with other security systems make it a leading solution in modern security technology.