Superior MotionCam (PhOD) Jeweller
Wireless PIR motion detector with extended photo verification possibilities

Expanded features, reliability, and compliance for PROs
Superior is a project-oriented product line. It includes advanced wireless versions of Jeweller devices. Experience exceptional features, cutting-edge hardware, improved certification compliance, effortless installation, and more.
The Superior difference
MotionCam (PhOD) Jeweller
Compliance with international security standards
No holding screw
Available for all PROs
Superior MotionCam (PhOD) Jeweller
Compliance with both international and local security standards
Holding screw for secured installation
Available only for accredited partners
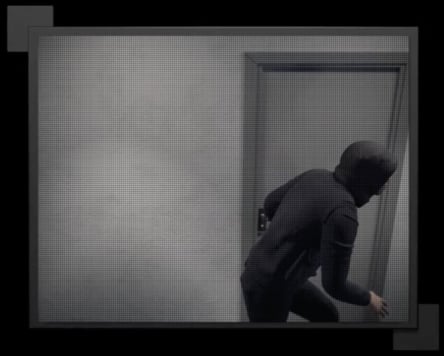
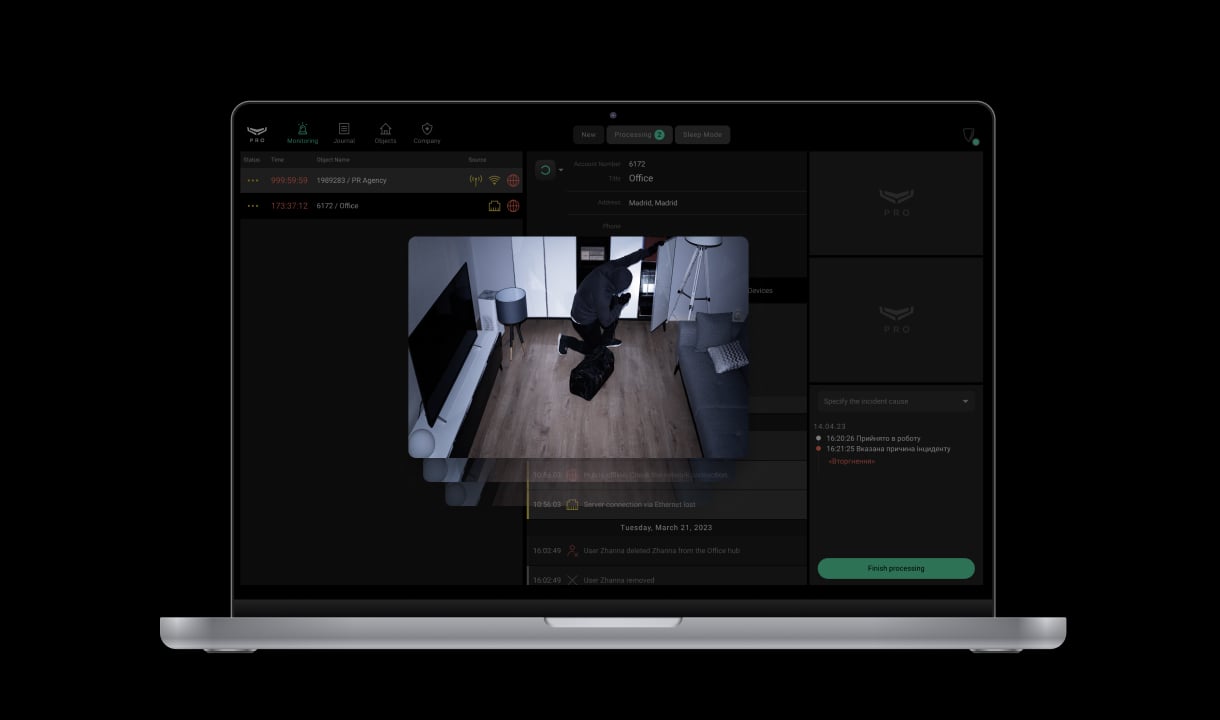
Lightning-fast alarms. Verified.
Superior MotionCam (PhOD) Jeweller has a built-in camera that takes photos once the detector is triggered. It needs just 9 seconds to show the actual situation on the scene. With visual evidence available in Ajax apps, the security company can quickly verify the threat and respond accordingly. Several types of photo verification relieve users of unnecessary anxiety and prevent security companies from false patrol calls. Users can take an on-demand photo with a single tap to monitor their house's state at any time. The detector can also automatically take photos by an alarm of another device in the system, by a specific schedule, and by arming/disarming.
Key features
In an Ajax system, you can combine devices of all product categories: Intrusion protection, Video surveillance, Fire and life safety, or Comfort and automation. Create the system to suit your needs and manage it in a single interface.
Wherever there is a risk of intrusion
Peace of mind on demand
The detector needs just a few seconds to show the actual situation on the scene and dispel the user's doubts in case of an alarm. It takes a click in the Ajax app to take an on-demand photo. Also, it can automatically take photos by schedule, by arming/disarming, or when another detector in the system is triggered.




Privacy first
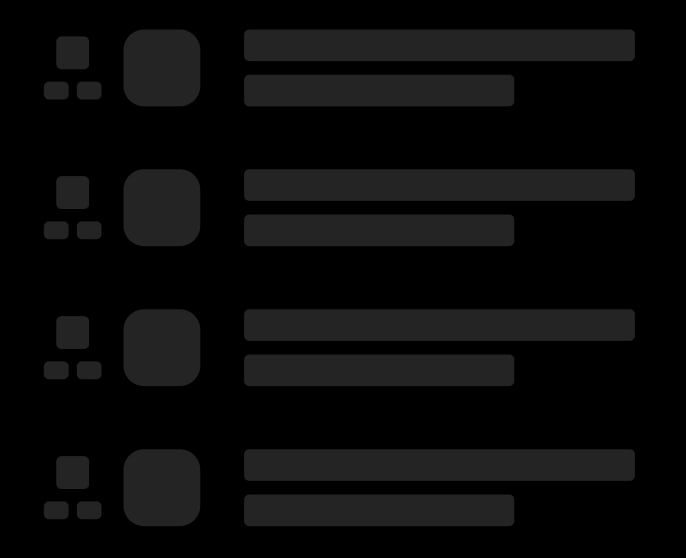


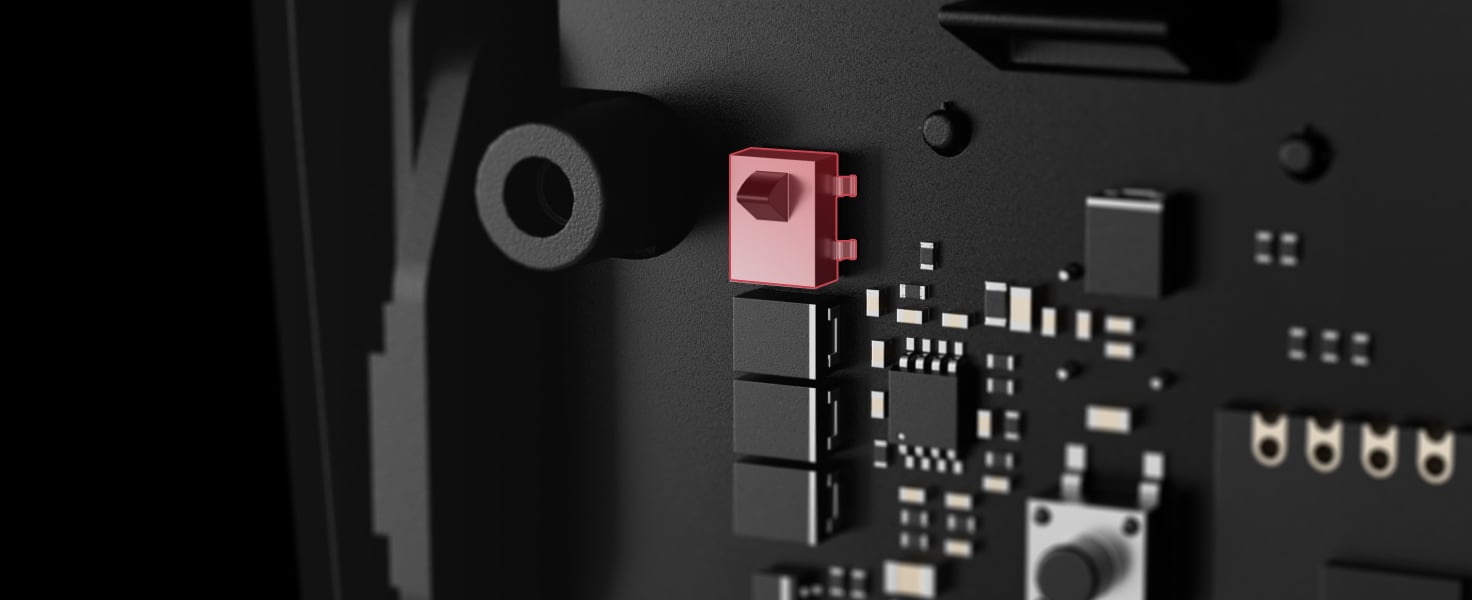
Discover future-proof hardware

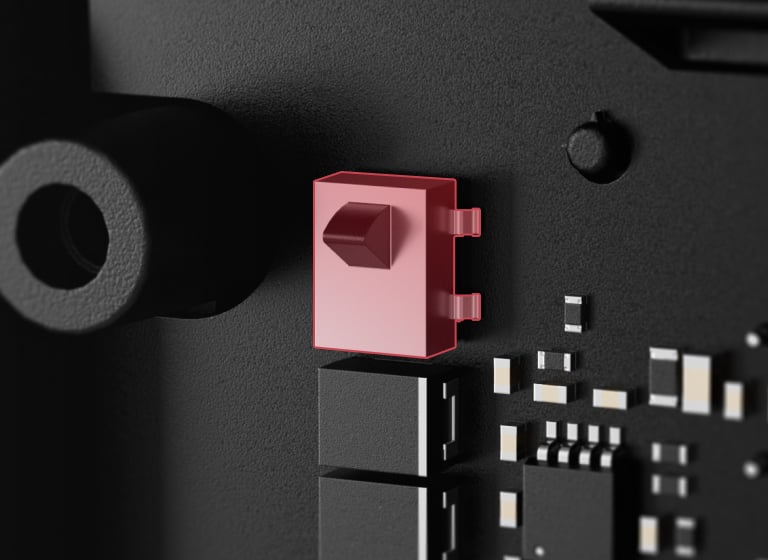
IR illumination for low light conditions
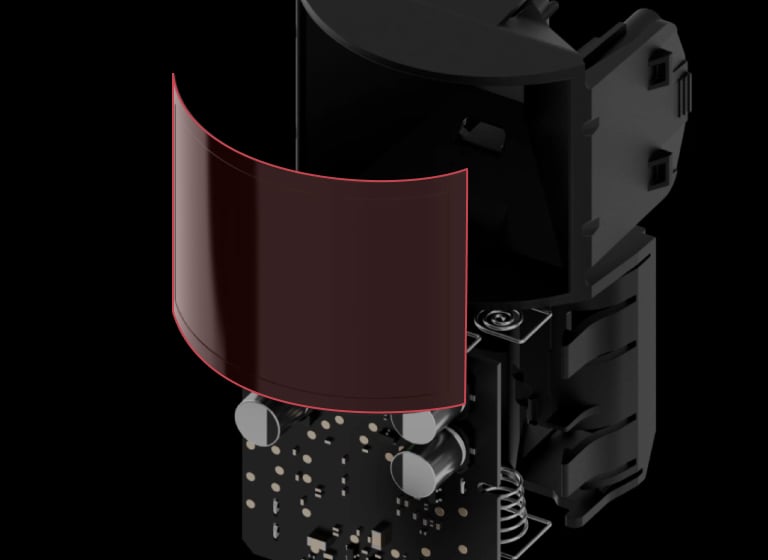
Fresnel lens

Camera

Enhanced battery
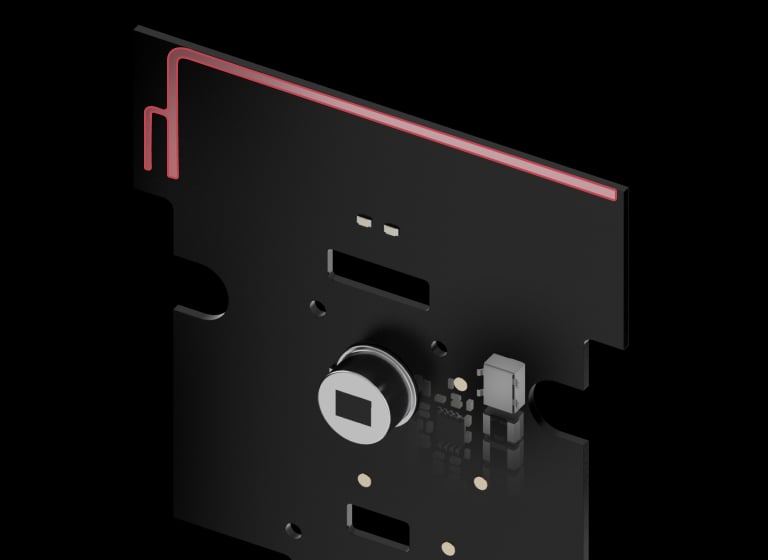
Jeweller and Wings antennas
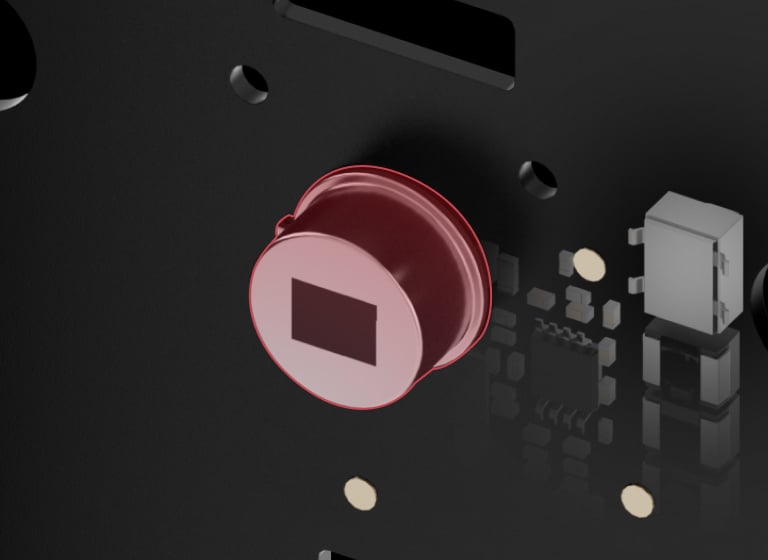
PIR sensor
Tamper
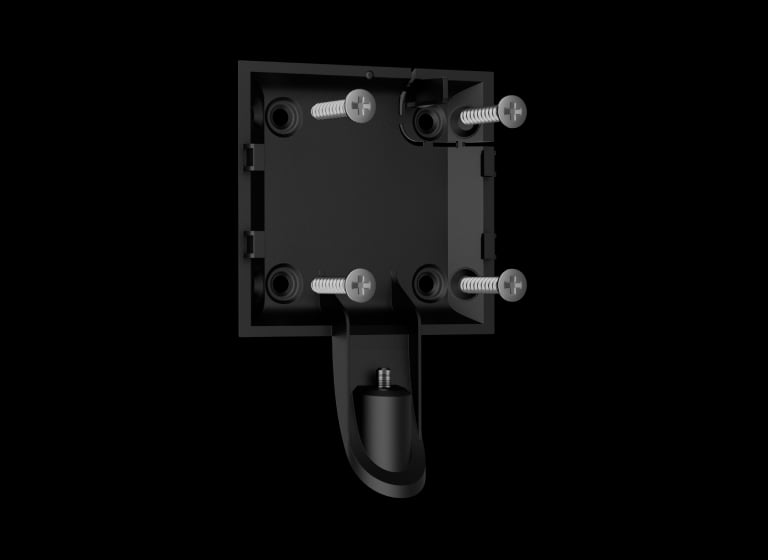
SmartBracket mounting panel

Holding screw to secure the detector on SmartBracket
No intruder goes unnoticed
PIR sensor
All Ajax motion detectors use PIR sensors by Excelitas Technologies — a field-leading American manufacturer specializing in designing and producing optronic components since 1931. Ajax Systems constantly proves the sensor's Superior quality at the production stage: we test 100% of manufactured devices. Wrapped into Ajax technologies, it brings the utmost accuracy of intrusion detection.

Special lens
The pattern of the Fresnel lens sections is designed to differentiate between the IR diagrams of a human, animal, and thermal noise. Large lens sections capture radiation at an adult's head and torso level. Smaller sections make the diagram more detailed. The lens provides the detector with accurate information about the thermal object in the detection zone and the nature of its movement.
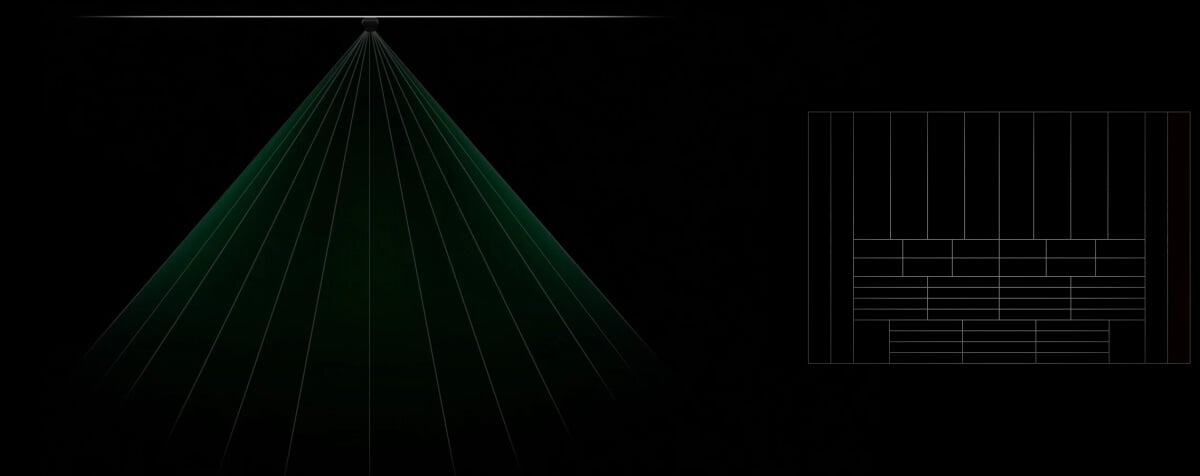
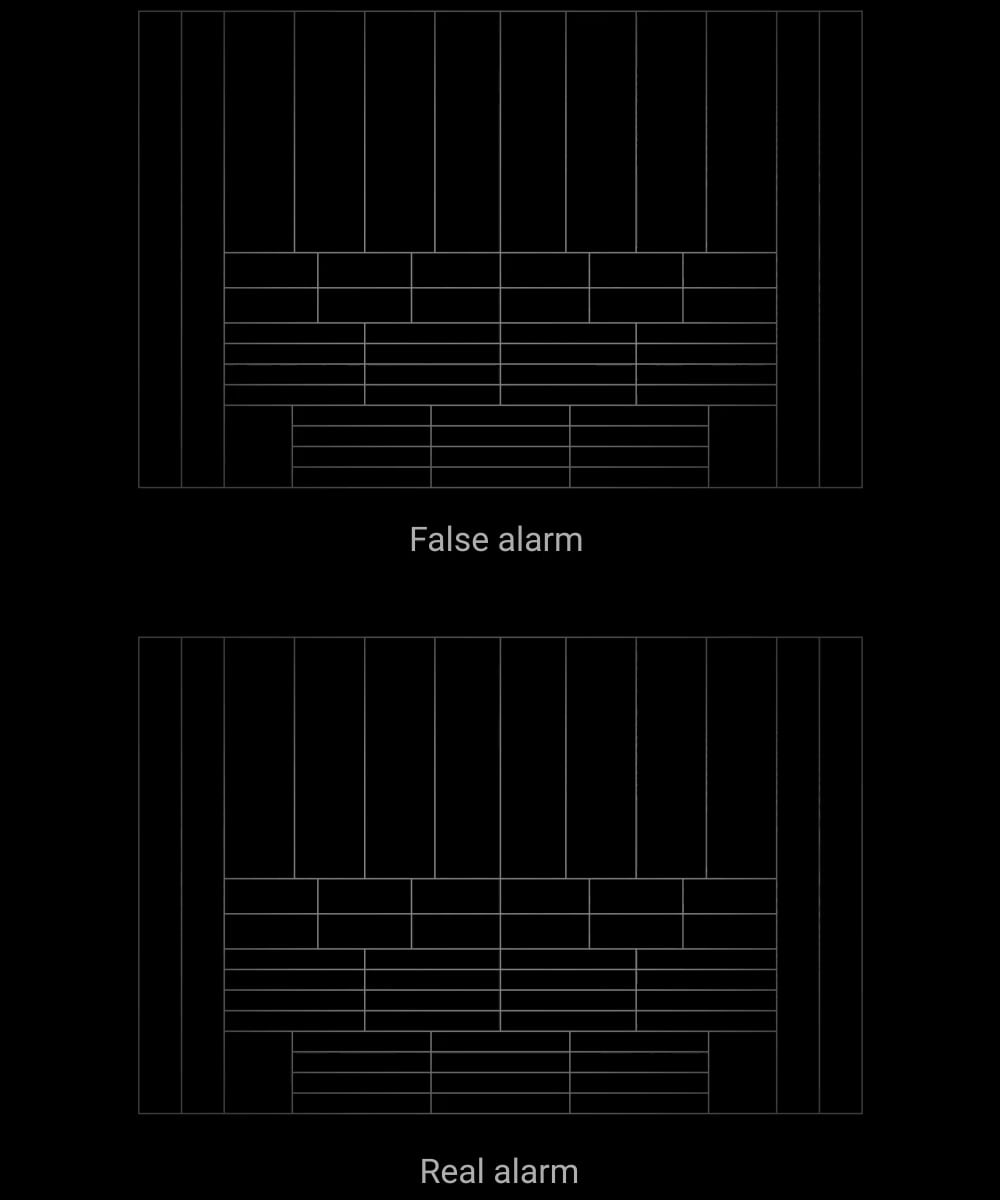
Thermal interferences filter

We processed thousands of thermal patterns caused by humans, animals, and the environment to develop the SmartDetect software algorithm. In armed mode, the detector constantly analyses the thermal diagram from the PIR sensor, including the IR radiation intensity, thermal spot size, movement speed, time spent in the detection zone, and other parameters. The algorithm identifies false alarm markers instantly and with high accuracy. As a result — the detector accurately responds to human motion without false alarms.
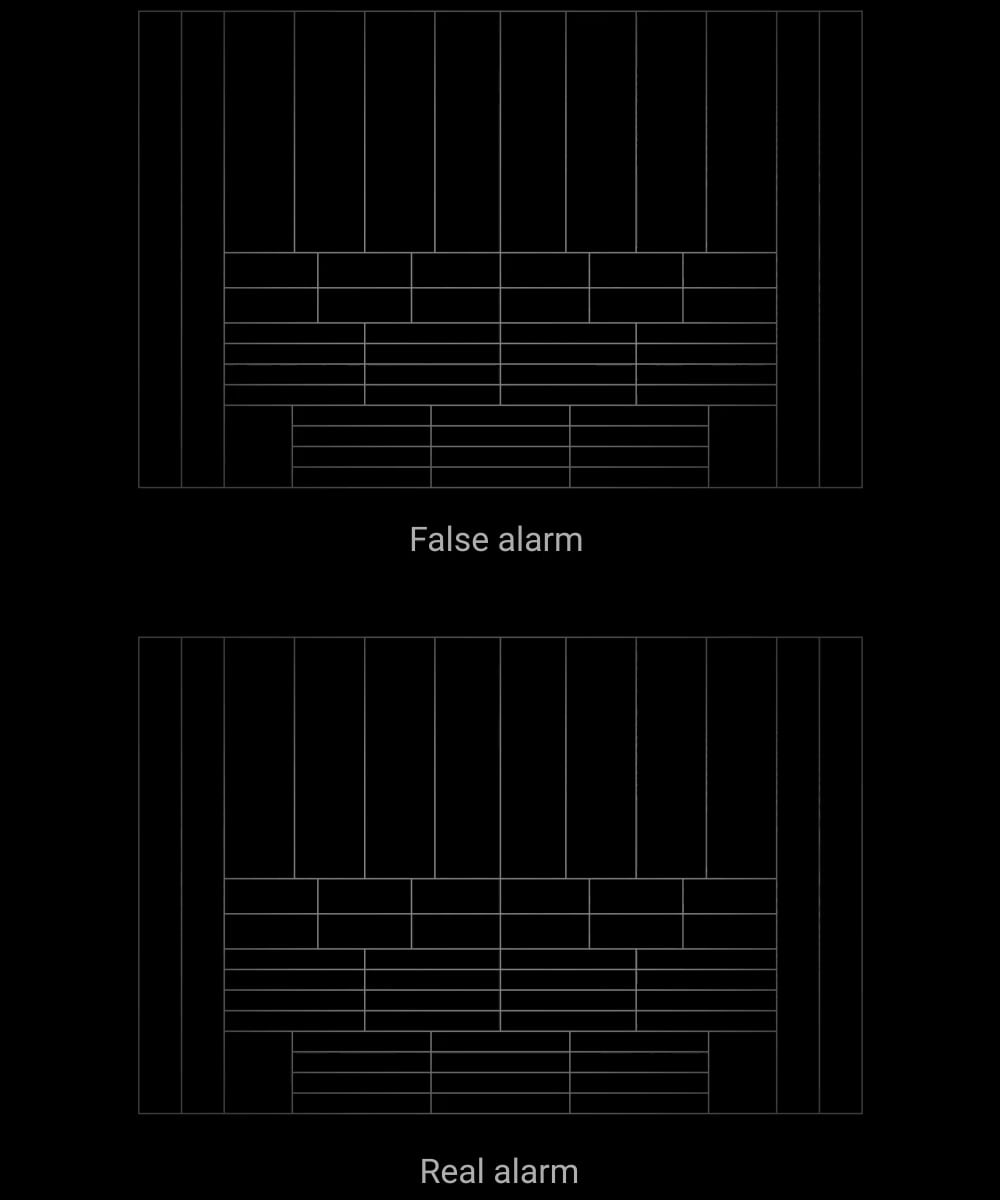
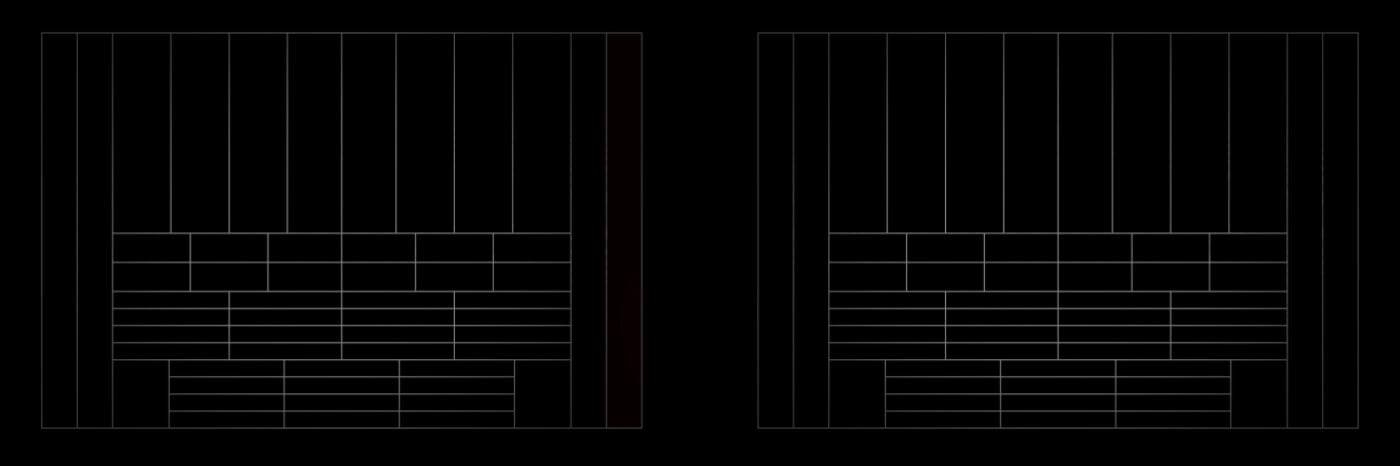
False alarm
Real alarm
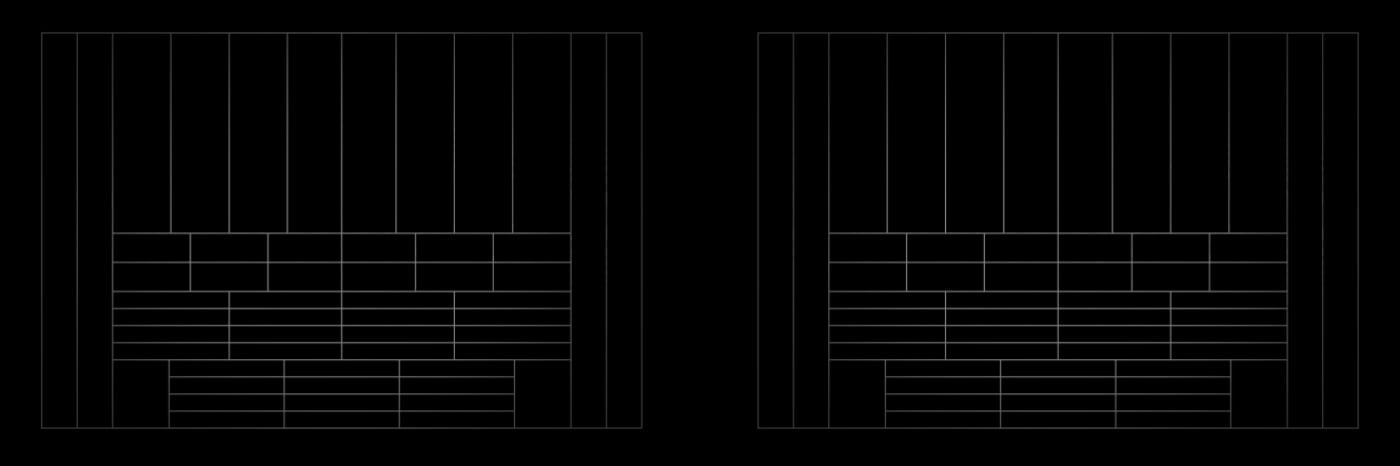
False alarm
Real alarm
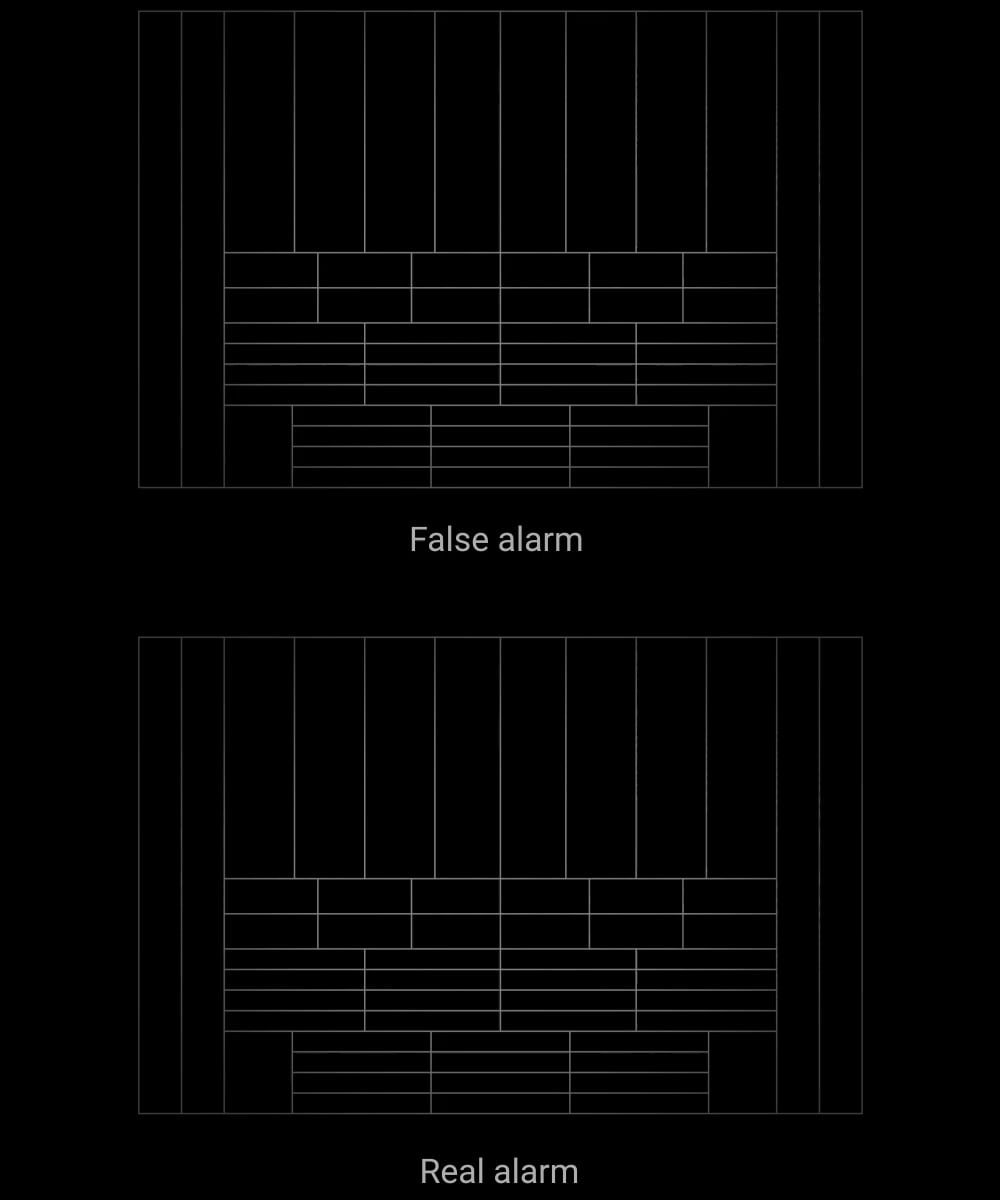
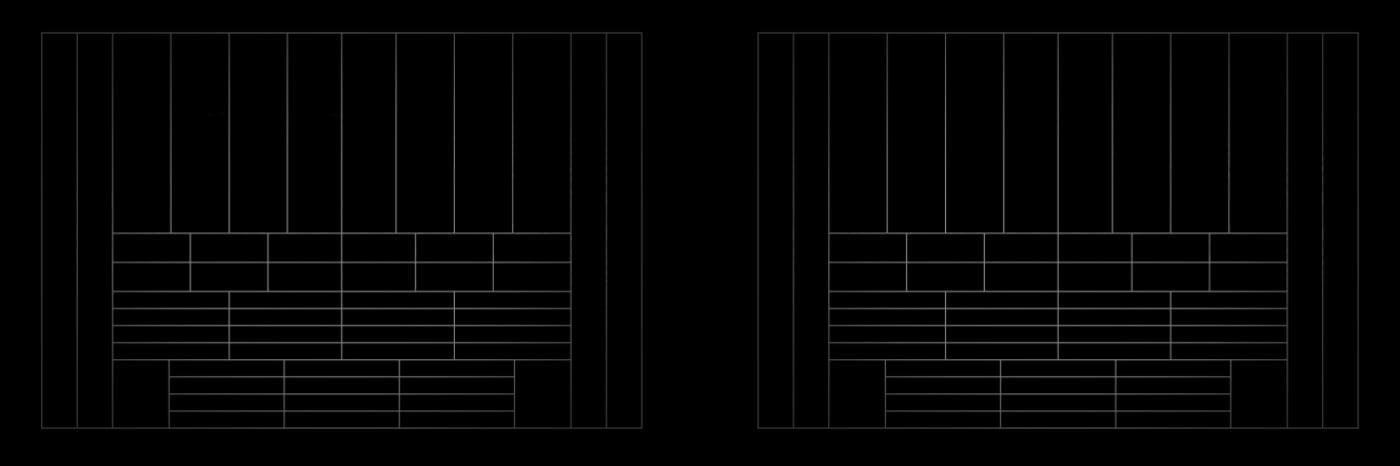
False alarm
Real alarm
Temperature compensation
Temperature compensation is a software mechanism keeping the thermal diagram contrast even if the ambient temperature is close to the temperature of the human body. With each ambient temperature measurement, the detector corrects the PIR sensor data according to the coefficient table stored in its memory. The detector is effective over the entire operating temperature range.
Sensitivity level
The detector can adapt to the conditions of a particular facility, considering possible thermal interference or pets. The sensitivity setting changes the set of markers by which false alarms are filtered. Low sensitivity makes the detector less likely to respond to an active pet. A high sensitivity will raise the alarm in case of any motion in the detection zone.
Professional installation
With the correct installation at the height of 7.9 ft and lens direction perpendicular to an alleged intrusion path, the detector provides an accurate thermal diagram and pet immunity. It instantly responds to a real threat, minimising false alarms caused by animals weighing up to 44 lb and below 1.6 ft in height.

Stable performance in heat and cold
The Superior devices are equipped with high-quality batteries from proven manufacturers only. In addition to real-time testing on the battery production stage, Ajax Systems inspects every unit to ensure the accuracy of the batteries’ characteristics. The temperature range does not affect the capacity, as the batteries provide stable performance in temperatures from 14 °F to 104 °F.
Minimal impact of threshold temperatures on battery life
High quality proven by regular tests
Up to 5 years of operation

Jeweller | Wings
Unique wireless technologies
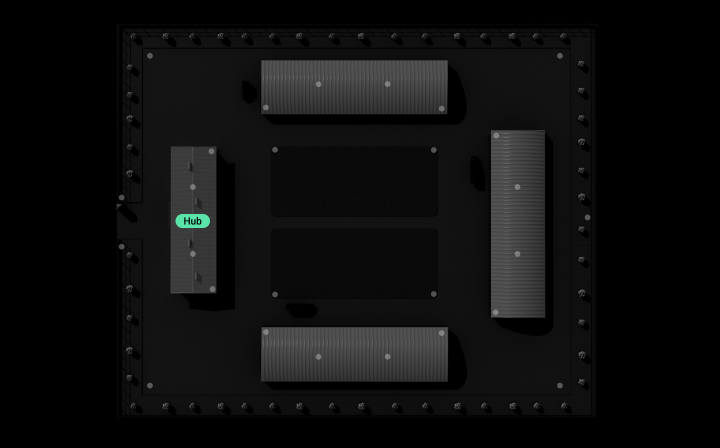
The Ajax system uses two-way secure radio communication based on Jeweller and Wings proprietary protocols. Radio protocols work in parallel and focus on their own function, guaranteeing instant data and delivery even with communication interruptions and a weak signal.
Up to 5,550 ft of radio communication with a hub or range extender3
Encrypted two-way radio communication
Notifications about jamming and connection loss
9 s to deliver the first photo1
Communication through steel and concrete
Some facilities have thick walls, metal partitions, or sheer distances that affect signal quality. Ajax range extenders are designed to increase the range of a wireless network and deliver stable connection with a hub despite the obstacles. And by choosing the model with an Ethernet cable connector, you get an additional communication channel. А single system can accommodate up to five range extenders.
Up to 5 range extenders within one system
Ethernet-equipped model available


System supervision
All Ajax devices perform automatic self-diagnosis and report their states to the hub. Essential parameters, including tamper, communication, power supply, and sensor statuses, are continuously monitored. The Ajax Cloud server controls communication between the hub and Ajax apps, ensuring instant notifications for ARCs, security companies, and users. In case of any malfunction or communication failure, an engineer is informed immediately to provide necessary services.
Automatic device self-diagnosis with status report
Regular polling to display the current device state on apps
Instant maintenance notifications

Sabotage-resistant




Effortless installation and setup
MotionCam S (PhOD) is ready to operate straight out of the box. Using the SmartBracket panel, an installer can effortlessly mount the device on the wall, eliminating the need to disassemble the enclosure. Ajax apps help quickly make the device a part of the ecosystem: simply pair the device with the hub by scanning the QR code. It can always be reconfigured remotely without the need for on-site visits.
Pairing with the hub via QR code

SmartBracket panel — no need to disassemble the enclosure
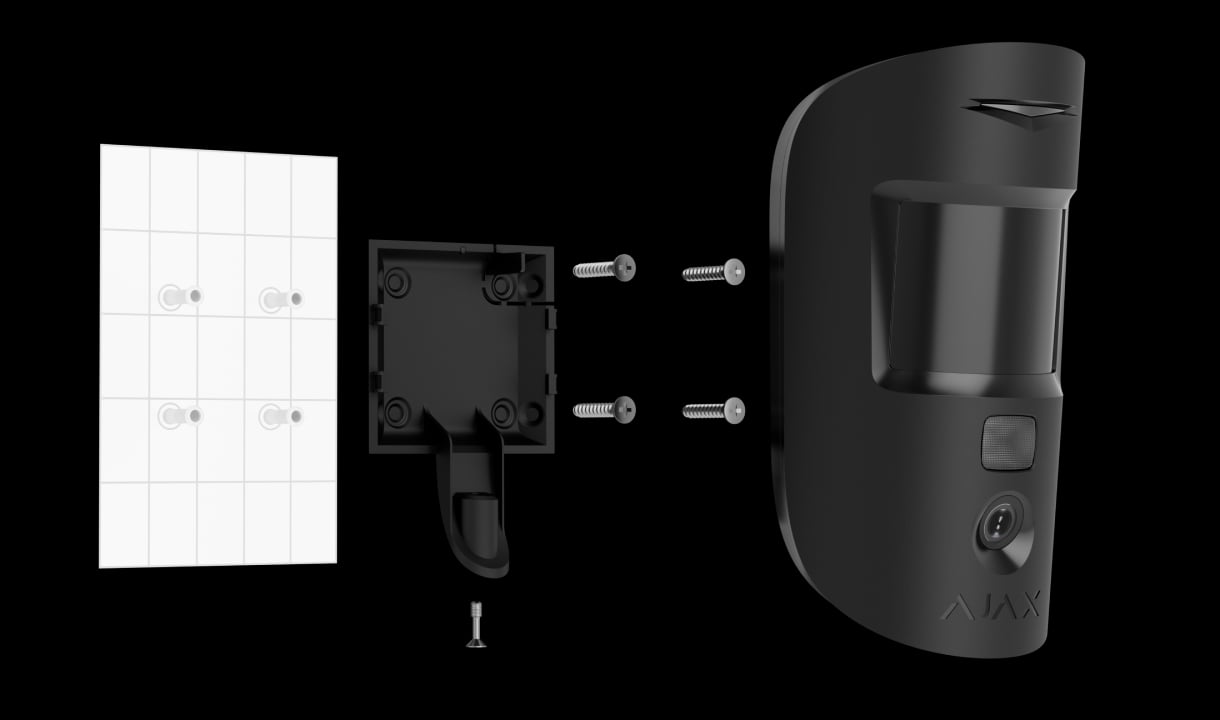
Configuring and testing in mobile and desktop apps
PRO Desktop app for macOS and Windows
- 1 — With default settings (photo resolution is 320 × 240 px).
- 2 — According to INCERT certification, detection range is up to 32.8 ft.
- 3 — In an open space.
Technical information
Superior MotionCam (PhOD) Jeweller
More MotionCam models
Ajax product categories
In an Ajax system, you can combine devices of all product categories: Intrusion protection, Video surveillance, Fire and life safety, or Comfort and automation. Create the system to suit your needs and manage it in a single interface.